How to Develop Your Risk Management Plan?
Within your Full Application, we ask you to identify, assess, and manage risks that may affect your proposed activities.
For this, we ask you to submit a risk register (or equivalent), assessing risks based on their likelihood and potential impact.
You may use your own risk register/risk management framework. If your consortium does not have one, you may use the DREAM 4 Health Risk Register Template.
Note:
- Upload one (1) file only (maximum size: 2MB).
- File name must follow this format: 15_ProjectRisk_RiskRegister.pdf.
How to use the risk register?
| The 'Name' field is a short risk title as a shorthand reference. |
| The 'Risk Description' field should set out a clear and concise description covering the cause, the risk event which the cause triggers and the consequence of the risk event. |
| The 'Risk Category' should identify the most appropriate risk category from the set of twelve options stated in SEA DREAM's Risk Management Framework. To see their definitions, check column B of the "3 Risk Category" sheet. |
| 'Status' denotes whether a risk is active or closed. A closed risk is one that has materialised (become an issue), has gone away or has been successfully treated. |
| The 'Proximity' field is the timeframe in which the risk might be expected to materialise. This is a best estimate. |
| The 'Likelihood' of individual risks is measured over the programme duration of a 5-year period. It is rated in five levels as follows:
|
| The potential 'Impact' of each risk is assessed using the Impact Assessment Scale which ranges from:
|
| 'Gross Likelihood' and 'Gross Impact' are the initial risk assessments before any risk treatment has been carried out and together make a composite Gross Risk Rating (Minor, Moderate, Major, Critical), which is auto-filled. |
| The 'Mitigation Strategy' sets out how the risk is being treated, while the following column is used to record any progress of implementing mitigation strategy (or any changes made to the mitigation strategy) in the next review periods. |
| 'Residual Likelihood' and 'Residual Impact' are the risk assessments after risk treatment and should be based on current progress in implementing mitigations, rather than future mitigations not yet implemented. These two together make a composite 'Residual Risk Rating', which is also auto-filled. |
| 'Risk Score' which determines the risk rating is calculated by multiplying the 'Likelihood' score and the 'Impact' score of a risk. |
| 'Trend’ indicates whether the risk is increasing, decreasing, or remaining the same compared to the last review. One of the three arrow signs should be selected from the drop-down list, whereas 'new' indicates newly identified risk. |
| 'Last Updated' refers to the date when the risk is last reviewed and updated on either the mitigation strategy or ratings. If the risk is reviewed but nothing is changed, the date should remain the same. |
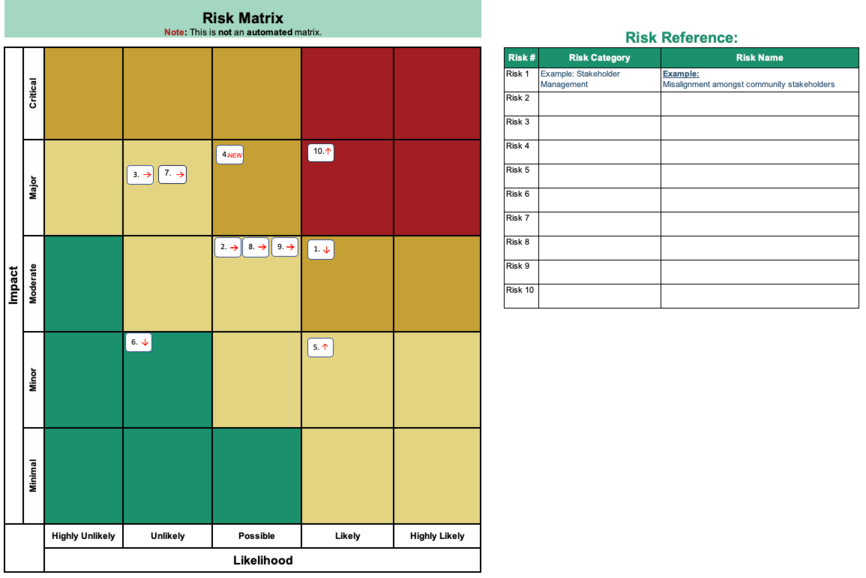
How to use the risk matrix?
This worksheet provides a visual overview of risks by mapping entries from the Risk Register based on their likelihood and impact. Applicants may use it to highlight and prioritise key risks—particularly the most critical ones.
The matrix also serves as a reference for how likelihood and impact scores combine to determine the overall risk rating.
Note:
- Use of the risk matrix is optional.
- The matrix is not automated and must be completed manually.
What are the risk categories?
The following definitions outline the 12 risk categories used across SEA DREAM. These categories are flexible and you may adapt these based on your context and needs of each consortium.
| Risk Category | Definition |
|---|---|
| Safety & Security | Risks related to the safety and security of the project environment, ranging from minimal safety concerns to critical situations involving actual harm and emergency interventions. |
| Stakeholder Management | Risks associated with stakeholder engagement and consensus, from productive collaboration to severe communication breakdowns and strained relations. |
| Finance, Fraud, and Fiduciary | Risks involving the mismanagement or misuse of financial resources, fraudulent activities, and failures in fiduciary responsibilities that could result in financial losses or legal repercussions. |
| Reputational Damage | Risks that could harm a project's and/or organisation's reputation, including negative publicity, public scandals, or association with unethical practices, which could lead to loss of trust and credibility. |
| Resourcing | Risks related to insufficient or inefficient allocation of human, financial, or material resources, affecting the ability to meet programme goals and objectives. |
| Safeguarding | Risks related to failures in protecting individuals, particularly vulnerable groups, from harm, including issues like whistleblowing, child protection, gender equality, sexual harassment, and bullying. |
| Information Security & Privacy | Risks associated with unauthorised access to, or loss of, sensitive information, leading to breaches of privacy, data theft, or legal violations. |
| IT & Systems | Risks involving the failure, disruption, or inefficiency of IT systems and infrastructure, which can impede operations, data integrity, and service delivery. |
| Contract Management | Risks arising from poor management of contracts, including non-compliance with terms, delays, cost overruns, or disputes with contractors. |
| Procurement | Risks related to the acquisition of goods and services, including supplier failure, non-compliance with procurement policies, and inadequate quality or cost-effectiveness. |
| Delivery | Risks that affect the successful delivery of the project including delays, cost overruns, or failure to meet quality and performance standards. |
| Monitoring, Evaluation, Accountability, and Learning (MEAL) | Risks associated with inadequate tracking, assessment, and learning from projects and programs, leading to ineffective decision making and missed opportunities for improvement. |
What are the impact definitions?
This table outlines how risks may be assessed across each category using the Impact Assessment Scale (Minimal to Critical). It provides general guidance on determining the severity of a risk’s potential consequences, which may be adapted based on the specific context of each project or consortium.
| Impact Definitions | |||||
|---|---|---|---|---|---|
| Risk Category | 1 Minimal | 2 Minor | 3 Moderate | 4 Major | 5 Critical |
| Safety & Security | The programme environment was generally safe and appropriate, measured actions taken. No harm occurred. | The programme environment was slightly unsafe but appropriate measures taken. No harm occurred but reporting required. | The programme environment is unsafe and though measures are taken these do not fully remove the risk. Although no harm occurs, it could occur if work continues. | The programme environment is unsafe and mitigating actions have limited effect. There is a security and safety event and actual injury and harm leading to medical intervention and/or assistance from authorities. | The programme environment is wholly unsafe and unsuitable for operations. There is actual injury and harm leading to the emergency involvement of the authorities and/or medical interventions. |
| Stakeholder Management | Stakeholders have alternative ideas, approaches and aims but are able to reach consensus and work together as a united front productively to meet objectives. | Stakeholders have differing ideas, approaches and aims but are able to reach consensus although this requires some additional effort, discussion and/or measures. Stakeholders are productive and objectives remain on track. | Stakeholders have differing ideas, approaches and aims and struggle to reach a consensus. The relationships and ways of working are often not aligned and have a moderate impact on productivity and objectives. | Stakeholders have wildly differing ideas, approaches and aims and often do not reach a consensus. The relationships and ways of working are not conducive to meeting the objectives and impact are being diminished. | Stakeholders are diametrically opposed to communication and collaboration. Relations are incredibly strained and when communication occurs, it is often counterproductive. Mediation attempts have failed and there may be recriminations. |
| Finance, Fraud, and Fiduciary | <2% of relevant budgeted forecast surplus, or expenditure have been exposed to financial, fraud, and/or fiduciary risks. | 2-5% of relevant budgeted / forecast surplus, or expenditure have been exposed to financial, fraud, and/or fiduciary risks. | 5-10% of relevant budgeted / forecast surplus, or expenditure have been exposed to financial, fraud, and/or fiduciary risks. | 10-15% relevant budgeted / forecast surplus, or expenditure have been exposed to financial, fraud, and/or fiduciary risks. | 15%+ relevant budgeted / forecast surplus, or expenditure have been exposed to financial, fraud, and/or fiduciary risks. |
| Reputational Damage | The incident remains internal, with negligible financial impact and no media attention. | Limited local media coverage with slight, short-lived damage to stakeholder trust. | Regional media attention with noticeable concern and moderate financial impacts. | Widespread media coverage causing significant trust loss and severe programme impacts. | Intense international scrutiny with irreparable trust loss and threats to organisational viability. |
| Resourcing | The project staff is adequate and the skillset appropriate. Objectives and targets are not hampered by a lack of resources. | The project staff is mostly adequate and the skillset mostly appropriate. Objectives and targets are not hampered by a lack of resources though economies are needed. | The project staff needs improvement and the skillset not typically relevant. Objectives and targets are slightly impacted by a lack of resources though on track. | The resources are having an obvious adverse effect on objectives and targets with the overall impact at stake. The staffing of the project needs immediate improvement, including the competencies. | There are insufficient resources with which to continue the project in its current form. The staffing of the project is insufficient. Reputational risks and the other risk areas are increasing as a result. |
| Safeguarding | Evidence that Safeguarding policies, protocols, and procedures are in place and is being verifiably complied effectively with no indication at all of any safeguarding breach. | Evidence that Safeguarding policies, protocols, and procedures are in place, and have been verifiably complied with fully but the effectiveness can be improved; no indication of any safeguarding breach. | Safeguarding policies, protocols, and procedures are in place, and are being followed but the application or implementation needs to be improved. No indication of any safeguarding breach resulting in harm, but improvement needed. Reporting to risk owner. | Safeguarding policies, protocols, and procedures cannot be verified. The potential for the risk of harm is introduced and action and further inquiries are needed. More information is needed to assess the situation properly. Immediate escalation to the focal point. | The risk of harm is being introduced and needs action and investigating. A safeguarding breach occurs. There is exposure to harm, reported harm and/or harm. Immediate escalation to the appropriate authority. |
| Information Security & Privacy | Informational governance is in place and staff experienced and trained to implementation, monitoring and updating systems. | Informational governance is in place and staff assigned to the implementation, monitoring and updating of systems. | Informational governance is in place, but staff need to improve on the implementation, monitoring and updating of systems. | Informational governance is not understood well and the implementation, monitoring and updating of systems is patchy, inconsistent, outdated and/or inaccurate leading to the possibility of breaches of regional regulations. | There are breaches of regional regulations regarding information security and privacy leading to possible or actual harm to institutions and individuals. Harm to operational, financial & fraud reputational, safeguarding and/or safety and security is a result. |
| IT & Systems | IT policies and systems are robust and secure, providing realistic control over threats and attacks, limiting vulnerabilities and loss. Downtime is minimal and productivity unimpeded. | IT policies and systems are all in place and the risk of threats and attacks, vulnerabilities and loss reduced. Downtime is rare and productivity maintained. | IT policies and systems are in place but the risk of threats and attacks, vulnerabilities and loss through inconsistencies of approach may lead to the loss of tangible and/or intangible assets, productivity and information security compromised. | Gaps or inadequate IT policies and systems expose the programme to threats and attacks, vulnerabilities and loss. Tangible and/or intangible assets, productivity and information security is compromised. | IT & Systems result in threats, attacks, vulnerabilities and loss. Harm to operational, financial & fraud, reputational, safeguarding and/or safety & security concerns is a result. |
| Contract Management | Contract management adheres to all relevant laws, regulations, policy and protocols and protects the contract holder helping to further fidelity, quality assurance and control and compliance. | Contract management follows all relevant laws, regulations, policy and protocols and protects the contract holder though fidelity, quality assurance & control and compliance may not be wholly assured. | Contract management follows all relevant laws, regulations, policy and protocols but the contract holder may not be fully immune to challenges and fidelity, quality assurance & control and compliance may be affected by delay or imprecision. | Contract management does not follow all relevant regulations, or policies and the contract holder may be open to loss and challenges. Fidelity, quality assurance & control and compliance cannot be upheld, and accountability and vulnerabilities increase. | Contract management is not compliant and causes the contract holder reputational and/or financial loss. Fidelity, quality assurance & control and compliance provisions are unsatisfactory leading to potential or actual breaches in Safeguarding, Fraud and aid diversion, corruption, Information Security & Privacy. |
| Procurement | The procurement processes for suppliers, vendors, and subcontractors, as well as the procure-to-pay (P2P) processes and contract registration, are implemented through the usual procedures. | Need identification is not predictive leading to tight turnaround timelines and pressure on drafting procurement documents and time for suppliers to respond. | Need identification is delayed or lags behind actual need leading to aggressive timelines and few quality bids, due to time constraints and low visibility. Single sourcing justifications are based on time constraints. | Low-quality and rushed procurement exercises result in delivery delays due to no/low quality/low number of bidders, low-quality partners, and low-quality work with poor VFM and reduced impact. | Inadequate need identification and rushed procurement prevents any key work from taking place. Any work commissioned damages the reputation of the Programme by introducing partners and service providers wholly unsuited/incapable of decent outputs. |
| Delivery | Implementation activity is undertaken with the necessary quality, fidelity, reaching the desired target group(s), and timelines outlined by implementers and evaluators and only negligible, slight limitations exist. | Implementation activity is undertaken with quality, fidelity, reaching desired target group(s), and timelines outlined by implementers and evaluators, but on-the-ground issues mean there are minor limitations, but within range. | Implementation activity is undertaken but there may be quality, fidelity, reaching desired target group(s), and timeline deviations. Work does not consistently hit targets (but are typically all around minimally acceptable levels). | Implementation activity is undertaken but cannot be easily aligned to the logframe or its benefit to the Programme may is negligible. The work does not meet minimally acceptable targets in key areas. There are questions on the quality, fidelity reach and timelines which raise questions on positive impact, opportunity cost and VFM. | The implementation work deviates from the Programme logframe, its benefit spurious, and is of extremely low quality as to cause disrepute. Work is partially complete with obvious and major fidelity of implementation and beneficiary flaws. Loss, diversion, corruption and waste issues are apparent. |
| Monitoring, Evaluation, Accountability, and Learning (MEAL) | MEAL work achieves the MEAL strategy aims with indicators, logframe and impact evaluation is based on comprehensive data collection and analysis. | MEAL work achieves MEAL strategy aims with monitoring, evaluation and learning phases of sufficient depth or breadth to adequately report on work confidently. The logframe and the data collection align, and the impact can be measured satisfactorily. | MEAL work achieves the basic functions (e.g., of a summary post-evaluation report demonstrating impact) but the monitoring, evaluation and learning phases may not be of sufficient depth or breadth to adequately report on work confidently. The logframe and the data collection may need further reconciling. | MEAL work is of low quality, and there are inconsistencies that have allowed data gaps and missed opportunities. Funders or clients may not have complete information to evaluate Programme work impact. | MEAL work is of poor quality, has major gaps, and is otherwise incomplete, inconsistent, incoherent. It has not provided funders or clients with basic information to justify cost outlay. Its reliability, validity and veracity may be questioned and repeated opportunities missed and unreported. |
What are the likelihood definitions?
This table provides guidance on how to rate each identified risk using the Likelihood Assessment Scale (Highly Unlikely to Highly Likely). It outlines the probability of a risk occurring over the grant duration, helping applicants assess and compare risks consistently.
| Likelihood Definition | ||||
| 1 | 2 | 3 | 4 | 5 |
| Highly Unlikely | Unlikely | Possible | Likely | Highly Likely |
| < 10% | 10-30% | 31-60% | 61-80% | > 80% |
| Likelihood measured over the programme duration | ||||
Workbook Management
The formulae in this workbook are not protected in order to allow the addition of new rows into the risk register. To add new rows, copy a complete blank row and use the 'Insert Copied Cells' command. This will replicate the formulae.
Source data for the formulae is included in a hidden worksheet called 'Cell data Don't Change'.
Subscribe To
Our Newsletter
Stay up to date with our latest funding,
news, events, and announcements.